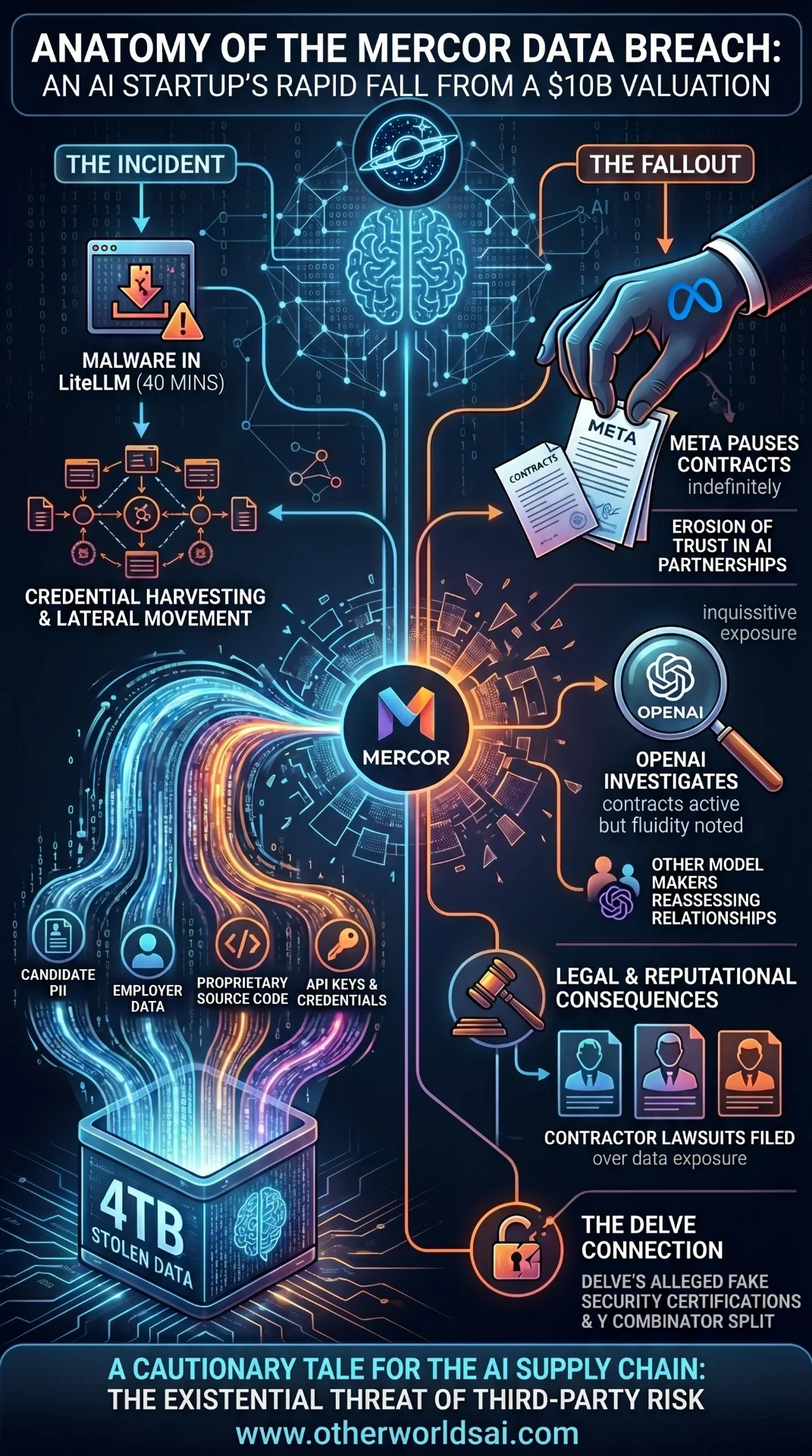
Mercor Data Breach: How a $10 Billion AI Startup's Worst Month Unfolded:
From a record-breaking Series C to a 4TB data breach, contractor lawsuits, and Meta pulling its contracts — here's everything that went wrong for Mercor in the span of just weeks.
The Rise Before the Fall: Mercor's $10B Valuation and AI Data Training Dominance:
Six months ago, Mercor was one of the hottest names in artificial intelligence. The AI data training startup had just closed a landmark $350 million Series C funding round, catapulting its valuation to a staggering $10 billion. Backed by some of the most prominent investors in Silicon Valley, Mercor had positioned itself as an indispensable partner to the world's largest AI model makers — handling sensitive custom datasets and proprietary training processes on their behalf.
The company's rise was nothing short of meteoric. Reports indicated Mercor was on pace to surpass $1 billion in annualized revenue earlier this year — a remarkable milestone for a startup still in its relative infancy. The demand for AI data training services was soaring, and Mercor sat squarely at the centre of that gold rush. Then, on March 31, everything changed.
The Mercor Data Breach Explained: What Happened and How It Began:
On March 31, Mercor publicly admitted it had become the target of a significant cybersecurity incident. The Mercor data breach was traced back to a compromise of LiteLLM, a widely used open-source tool that is downloaded millions of times per day. For a window of approximately 40 minutes, LiteLLM harboured credential-harvesting malware — rogue software designed to steal login credentials from unsuspecting users and systems.
The attack escalated quickly through a chain-reaction of compromised access. Stolen credentials were used to gain entry into additional software and accounts, which in turn yielded more credentials, and so on — a classic lateral movement attack pattern that allowed bad actors to burrow deeper into connected systems. The vulnerability in a single open-source dependency had opened a door into one of the AI industry's most data-rich companies.
4TB of Stolen Data: What the Hackers Claim to Have:
In the weeks following the initial disclosure, a hacker group emerged claiming to have extracted a staggering 4 terabytes of data from Mercor's systems. The alleged stolen data reportedly includes:
· Candidate profiles and personally identifiable information (PII)
· Employer data and business records.
· Proprietary source code.
· API keys and sensitive authentication credentials.
Mercor has not confirmed or denied the authenticity of the claimed data. The company issued a measured statement, saying it is "investigating and will continue to communicate with our customers and contractors directly as appropriate and devote the resources necessary to resolving the matter as soon as possible." For a company handling some of the AI industry's most closely guarded secrets, however, the ambiguity itself has been damaging.
Meta Pauses Mercor Contracts: The Fallout Begins:
The most significant confirmed consequence of the breach came from Meta. Sources revealed to Wired that Meta has indefinitely paused its contracts with Mercor following the cybersecurity incident. Mercor declined to comment on the report to TechCrunch.
The significance of Meta's decision cannot be overstated. Earlier this year, Meta made headlines when it spent $14.3 billion to acquire Mercor competitor Scale AI. Despite that enormous investment in a rival firm, Meta had continued working with Mercor — a testament to how central Mercor's services had become to Meta's AI development pipeline. The decision to pause those contracts signals a serious erosion of trust.
The Hidden AI War
Nobody Is Telling You About
Our latest documentary deep-dive into the geopolitical struggle for machine intelligence dominance. Explore the two paths of AI development: open source vs. closed architecture.
AI data training companies like Mercor are entrusted with their clients' most sensitive intellectual property. These aren't just vendor relationships — they involve custom datasets, proprietary model training processes, and the kind of competitive intelligence that companies spend billions to develop and protect. A breach of Mercor's systems is, in effect, a potential breach of every client it serves.
OpenAI Investigates; Other Model Makers Weigh Their Options:
OpenAI confirmed to Wired that it is actively investigating its potential exposure in the Mercor data breach. Crucially, OpenAI stated that it had not paused or ended its contracts with Mercor at the time of reporting — a small but notable vote of continued confidence.
However, the situation remains fluid and potentially more widespread. Multiple sources have informed TechCrunch that other large AI model makers may also be reassessing their relationships with Mercor in the wake of the breach. While TechCrunch has not yet confirmed enough details to name specific companies, the signal from across the industry is clear: trust in Mercor's data security has been shaken, and clients are conducting their own internal risk assessments.
Contractor Lawsuits Filed Over Personal Data Exposure:
Beyond the corporate fallout, Mercor is now also facing legal action from the individuals whose data may have been exposed. According to Business Insider, five of Mercor's contractors have filed lawsuits over alleged personal data exposure arising from the breach. Whether these suits represent a serious long-term legal threat or are primarily opportunistic filings remains to be seen, but the optics compound an already difficult public relations situation for the startup.
One lawsuit reviewed by TechCrunch takes an unusually broad approach to assigning liability. It names not only Mercor, but also LiteLLM and Delve — an AI compliance startup — as defendants. The reasoning is novel, if ambitious: Delve had provided LiteLLM with its security certifications, and an anonymous whistleblower has accused Delve of allegedly faking data for those certifications and using rubber-stamping auditors.
The Delve Connection: Fake Security Certifications and the Y Combinator Split:
Delve's alleged misconduct adds a disturbing additional layer to the Mercor data breach narrative. A security certification is not a guarantee against attacks, but it is meant to signal that a company has robust processes in place to detect, prevent, and respond to threats. If those certifications were issued fraudulently or without rigorous auditing, the entire security assurance chain is compromised.
Delve has denied the allegations, though it has simultaneously instituted operational changes. The controversy has nevertheless taken a severe toll: Y Combinator, the prestigious Silicon Valley accelerator, severed its ties with Delve amid the growing scandal. In the startup world, a YC break is more than symbolic — it carries reputational weight that shapes investor and partner confidence.
LiteLLM has since moved on. The open-source tool dropped Delve as its compliance partner and has engaged another AI compliance startup to obtain fresh security certifications. LiteLLM also published a comprehensive public report detailing the security incident, offering a level of transparency that stands in contrast to the relative silence from Mercor itself. Notably, Mercor has confirmed to TechCrunch that it was not itself a Delve customer — meaning the certification chain issue is one step removed from Mercor's own compliance posture.
What This Means for AI Data Security and the Broader Industry:
The Mercor breach is a cautionary tale for the entire AI supply chain. As AI model training becomes increasingly outsourced to specialist firms, the attack surface for sensitive intellectual property expands. A vulnerability in a widely-used open-source library — exploited for just 40 minutes — was enough to potentially expose the crown jewels of multiple billion-dollar AI companies.
The incident raises urgent questions about third-party risk management in the AI industry. When AI companies delegate model training to external partners, they are implicitly extending their own security perimeter. Vetting vendors not just on capability but on cybersecurity posture — including their own supply chain dependencies — is becoming an existential imperative.
For Mercor specifically, the path forward is steep. With over $1 billion in annualized revenue reportedly at risk, the company must simultaneously manage an active investigation, restore client trust, navigate multiple lawsuits, and rebuild its reputation as a secure handler of sensitive AI data — all under intense public and industry scrutiny.